MITRE ATT&CK TTP Report
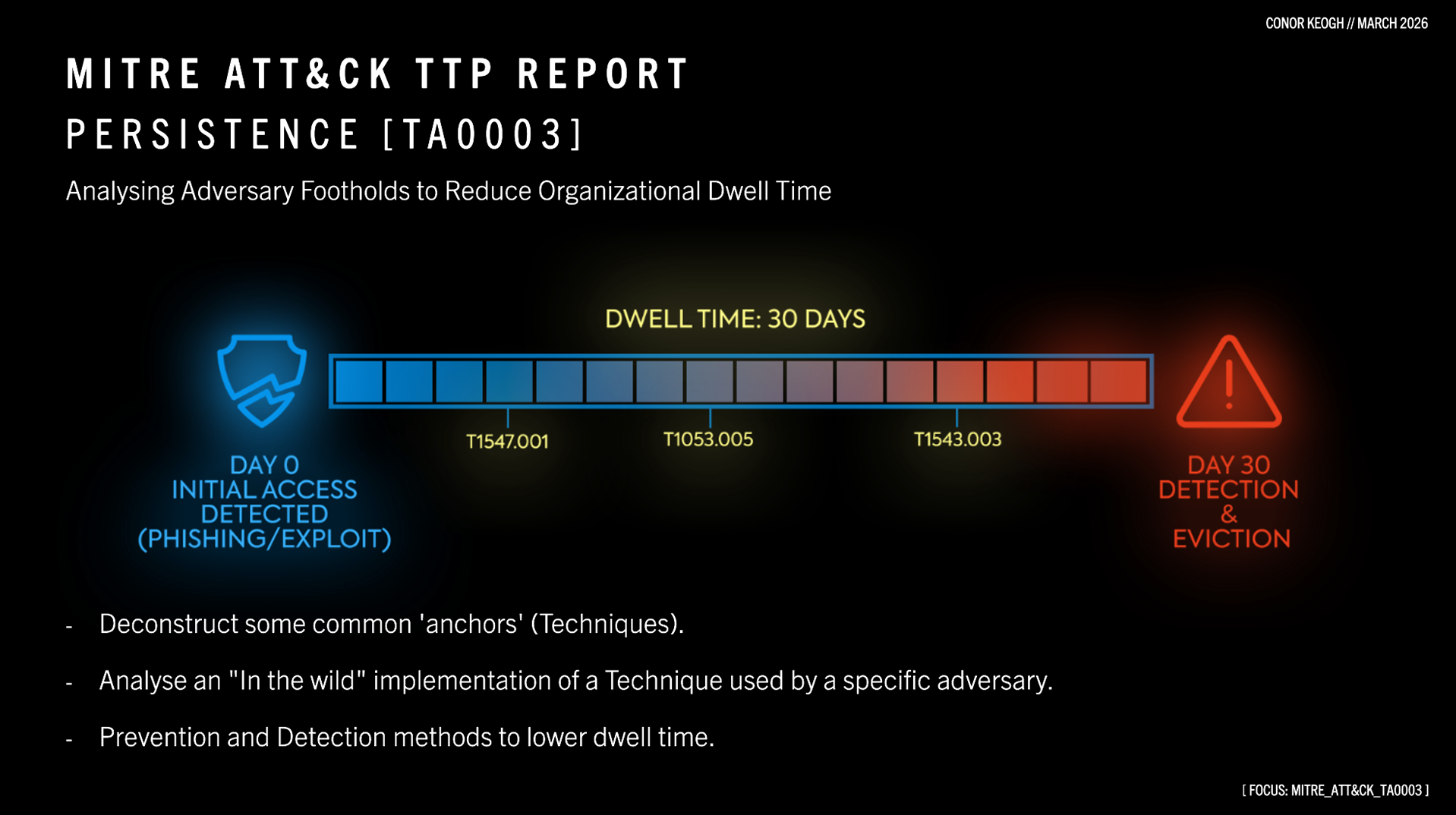
1. Persistance [TA003]

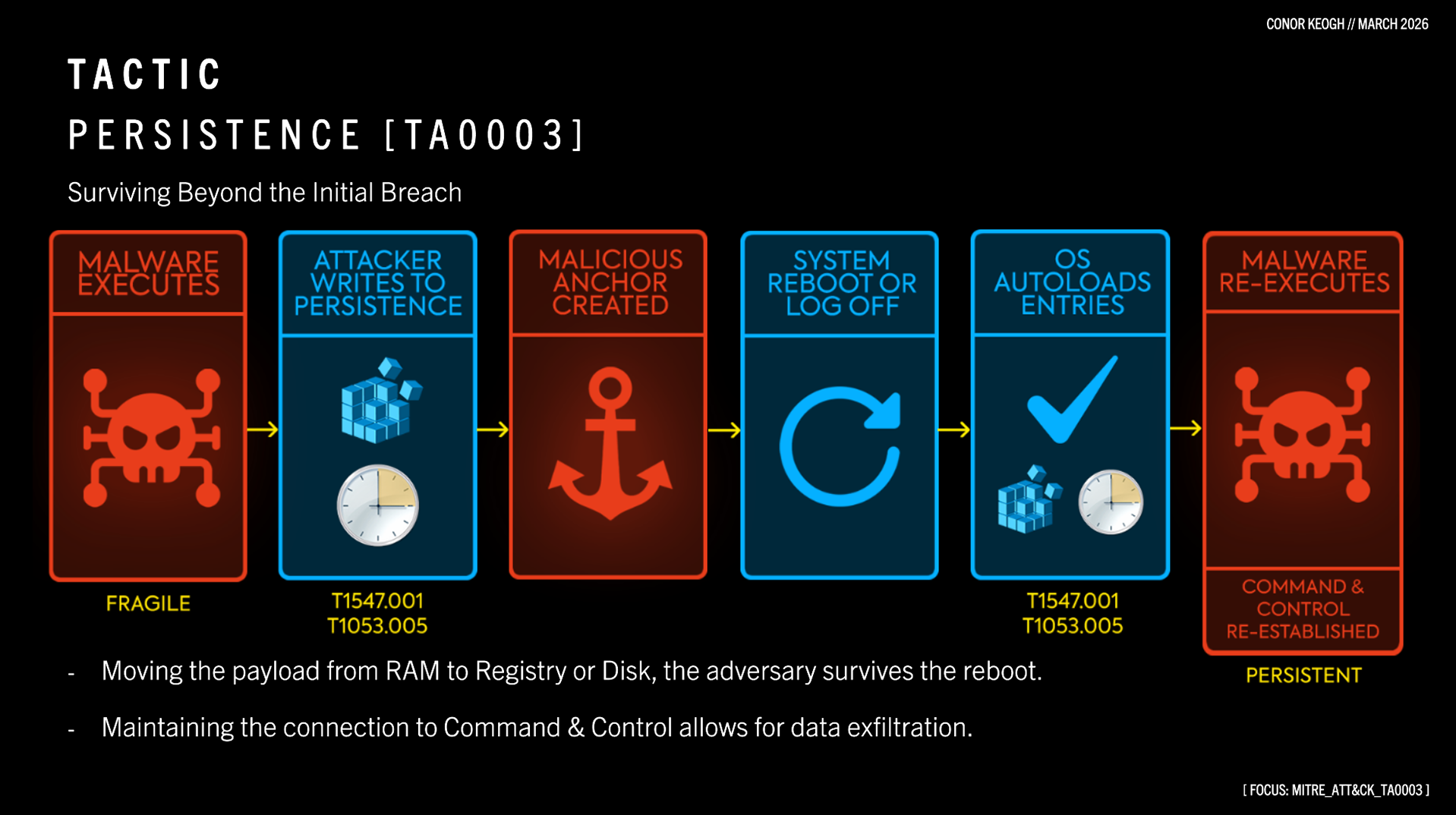
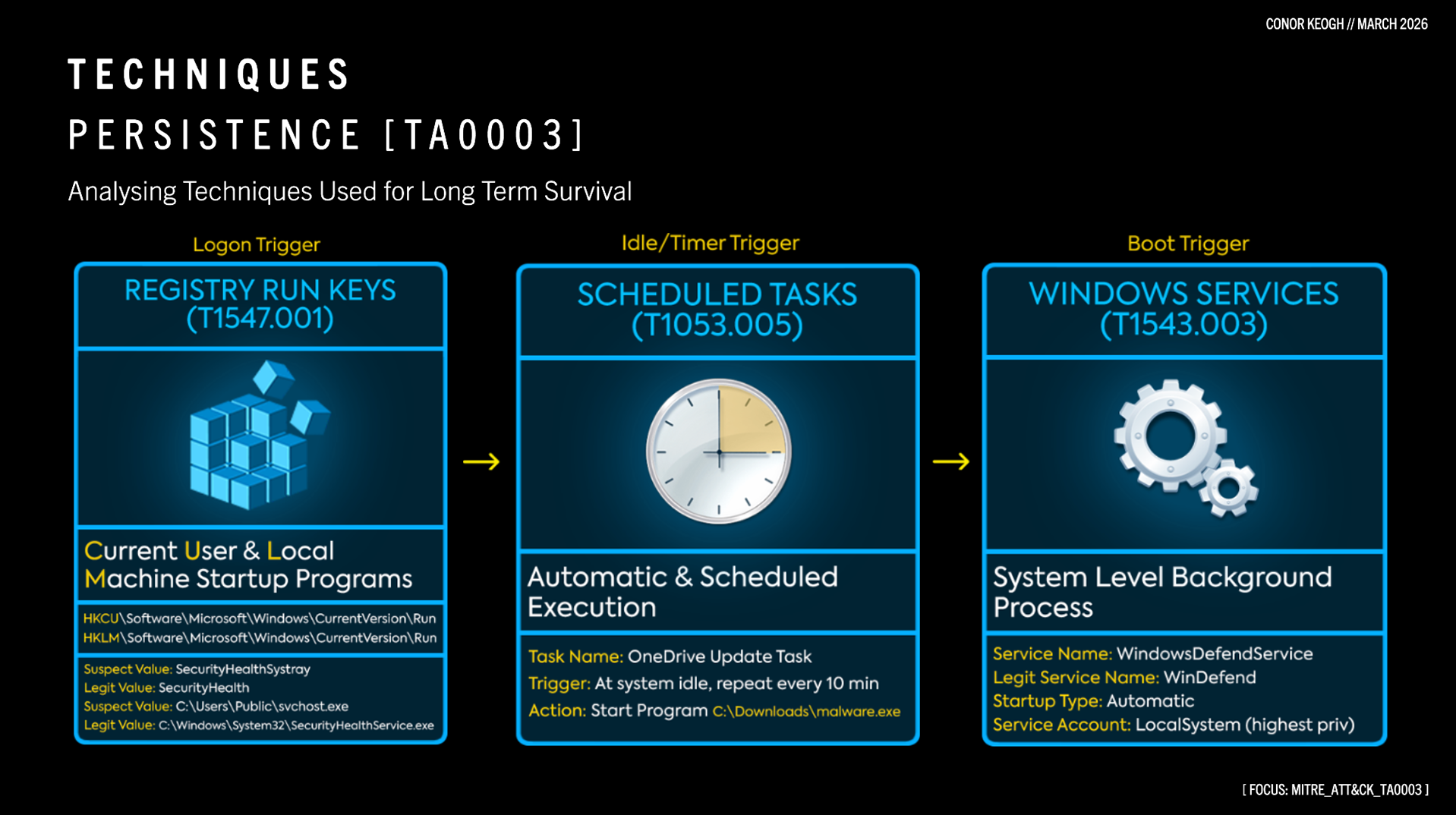
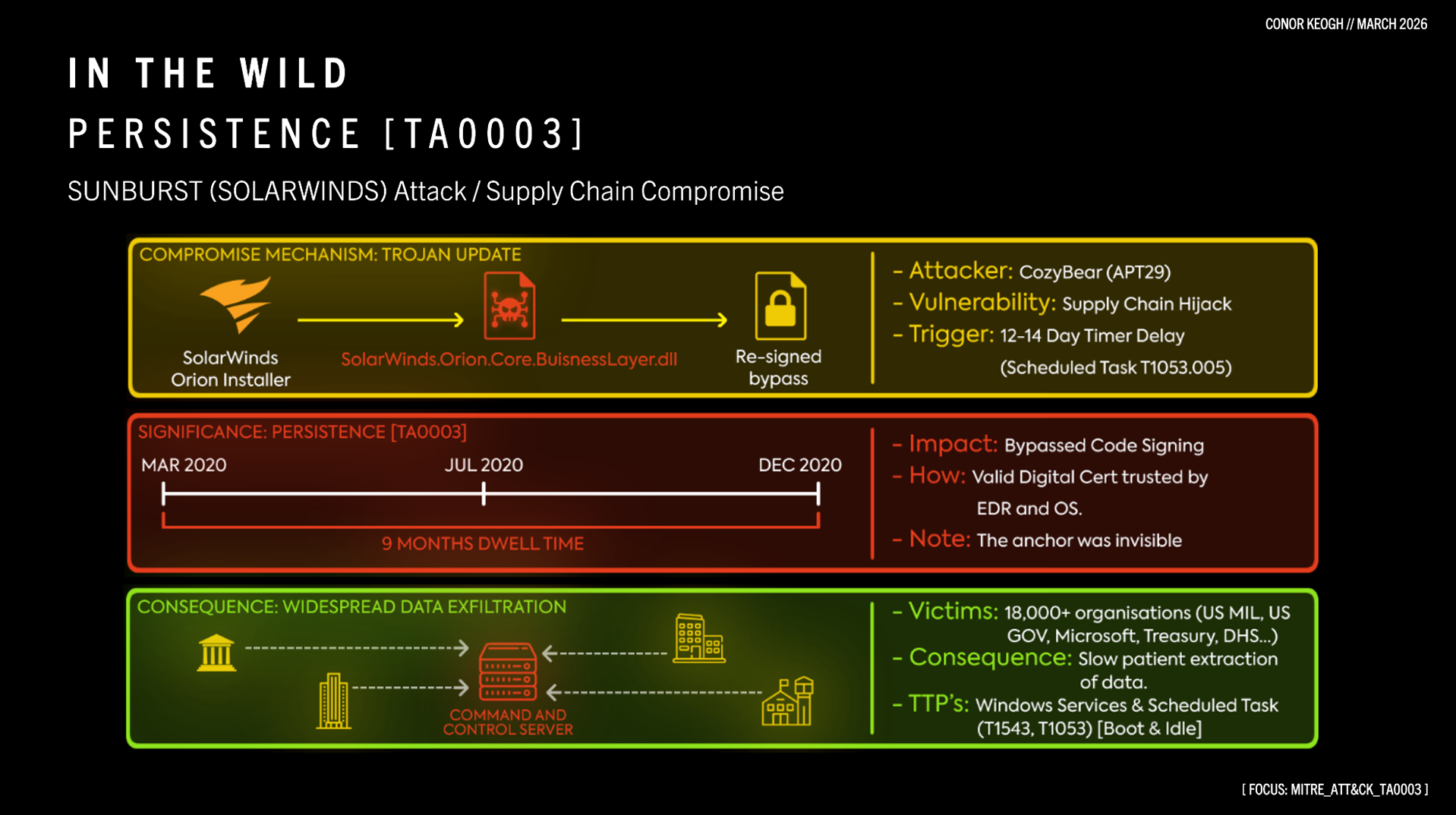
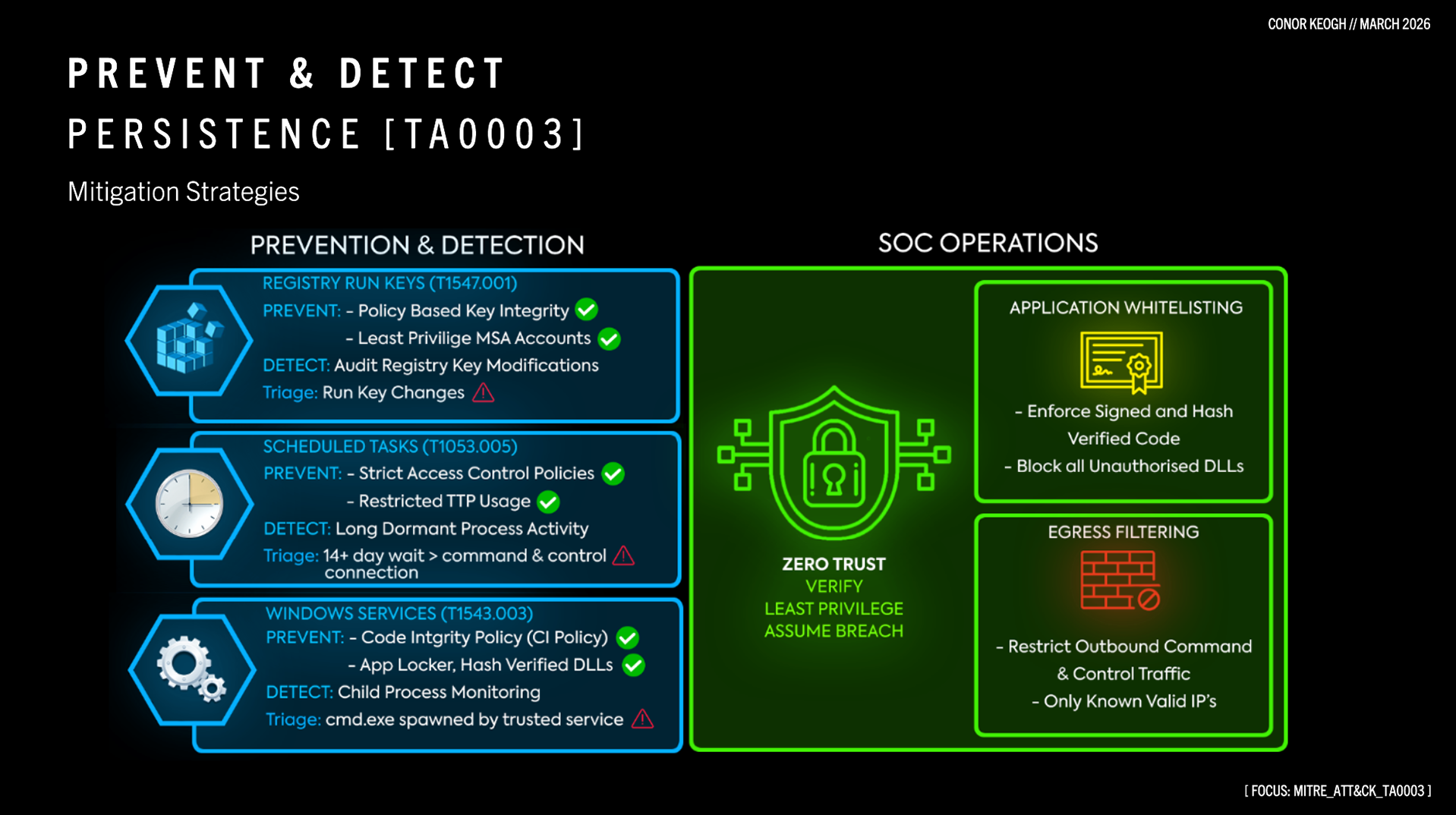
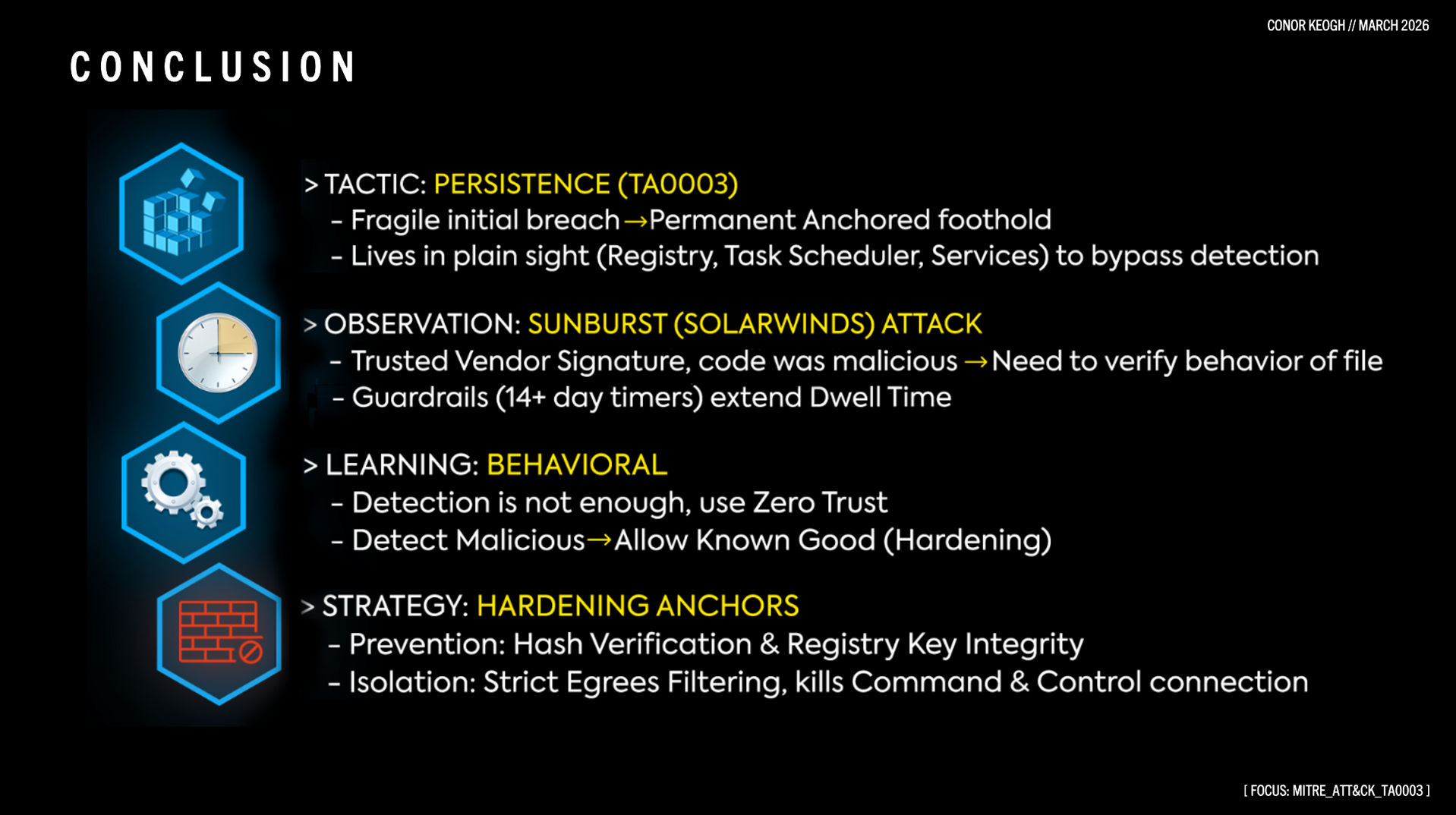
An analysis of MITRE ATT&CK Tactic TA0003. This project explores how attackers weaponize administrative trust to bypass detection, focusing on the failure of traditional code-signing in the SUNBURST breach and the implementation of AppLocker and Egress filtering as critical mitigations.
Developed as a capstone briefing for a high-intensity Cybersecurity Bootcamp, this project was presented at State Street Kilkenny to demonstrate technical mastery of the MITRE ATT&CK framework. The presentation synthesizes the mechanics of Windows-based persistence with a strategic analysis of the SUNBURST (SolarWinds) supply chain breach